SSL is touted as the golden bullet of assurance of website identity, and while there is no doubt that SSL can play a significant role, it's certainly not bulletproof as is shown by this Washington Post article and this cnet.com article.
So SSL encryption can't tell you if you have been sent to the correct site, it only tells you if the DNS (looked up from your machine) matches the name in the certificate. This is a real weakness if someone has poisoned your view of the DNS and this is possible as the DNS is not secure.
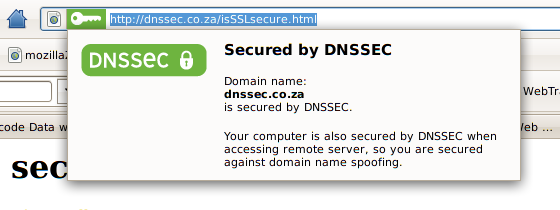 So SSL would work better if DNS were secured - thats true. Well, we are
getting there, albeit slowly.
DNSSEC has been around for years but
only now is it beginning to gain momentum. There is lots of
software available including
plugins for Firefox that'll
notify
you whether the DNS is secure for the site you are on.
So SSL would work better if DNS were secured - thats true. Well, we are
getting there, albeit slowly.
DNSSEC has been around for years but
only now is it beginning to gain momentum. There is lots of
software available including
plugins for Firefox that'll
notify
you whether the DNS is secure for the site you are on.
Its also possible to revocate an SSL certificate but unfortunately the most widly used browser, Internet Explorer, has this feature switched off by default thus allowing compromised certificated to still be used.
A number of Web Sites have "Self-Signed" certificates - this leads to Users becoming conditioned to simply accepting Web Certificate credentials - thats assuming they even look at Padlocks or other security icon on the Page. The Green or Blue URL bar has made it easier for users to see at a glance that the site they are on is SSL protected and its here that the DNS Key is also displayed.